Category: Secure File Transfer
-

Key provisions of the Trans-Pacific partnership
Overview The Trans-Pacific Partnership has drawn a tsunami of reactions both for and against it. For sure, it’s going to be a…
Learn More
-

SSL vs SSH – a Not-So-Technical comparison
Overview The most widely used secure file transfer protocols, SFTP and FTPS, get their security from underlying protocols. SFTP from SSH and…
Learn More
-

Adding email notification to a file transfer server antivirus upload scan
Overview When your server antivirus detects malware infection on a recent file upload, what would you like it to do? In our…
Learn More
-

Automating an upload virus scan using a windows file transfer server and kaspersky
Overview A couple of years ago, we wrote a 3-part tutorial showing how you could automate FTP virus scans with Kaspersky Antivirus.…
Learn More
-

How to use a windows FTP client for secure downloads
Despite FTP’s vulnerabilities, many Windows users still use FTP clients for transferring files over the Internet. If you really have to keep…
Learn More
-
SSL vs. TLS | Knowing the Difference Between SSL and TLS
SSL vs. TLS Overview SSL and TLS have many similarities. That’s why, in most software applications, they’re configured together as “SSL/TLS”. However,…
Learn More
-

Demystifying SMTP ports: when to use port 25, 587, 465 or 2525
When you’re tasked with configuring Simple Mail Transfer Protocol (SMTP) settings to connect to an email server, you need to get two…
Learn More
-

What is two factor (2 step) authentication?
Overview Passwords (even strong ones) can sometimes fall into the wrong hands. To minimize the risk of granting access to an impersonator…
Learn More
-

7 things CEOs can do to stay clear of the waves of data breaches
Overview The departure of Avid Life Media (Ashley Madison’s parent company) CEO Noel Biderman wasn’t the first time an executive resigned due…
Learn More
-

What is a key exchange?
Overview Before any files can be securely sent over protocols like FTPS, HTTPS, and SFTP, the two communicating parties must engage in…
Learn More
-

Understanding the limitation of IRS’ “Get transcript” Multi-Step authentication
Overview The multi-step authentication system used to secure the IRS “Get Transcript” application required several pieces of data that only the taxpayers…
Learn More
-

A key takeaway from the IRS data breach
Recently, we learned that the total number of accounts that may have been compromised in the IRS data breach might have exceeded…
Learn More
-
SCP vs. SFTP: 9 key comparisons
Secure Copy Protocol (SCP) and Secure File Transfer Protocol (SFTP) are both widely accepted alternatives to the enduring but highly vulnerable File…
Learn More
-

SMTP vs IMAP vs POP3 – knowing the difference
Overview Your ability to send and receive emails is largely due to 3 TCP protocols: SMTP, IMAP, and POP3. If you’ve got…
Learn More
-

How to use public key authentication with partners
Overview Several months ago, we published a tutorial crafted to help network/server administrators prepare trading partners for SFTP automation. That article lacked…
Learn More
-

12 file transfer protocols for businesses
Overview: File Transfer Protocols for Businesses Still wondering which file transfer protocol is right for your business? Here are a dozen you…
Learn More
-

Various linux SCP examples to get you started with using secure copy
Overview SCP (Secure Copy) is a quick, easy way to transfer files securely between two Linux machines. If you don’t mind using…
Learn More
-

5 questions every CEO should ask about company file transfers
Overview Most chief executive officers would have no time to scrutinize their organization’s file transfer activities. That’s bound to change once they…
Learn More
-

How to import a client certificate to firefox
Overview Client certificate authentication is very suitable for highly secure HTTPS connections. But for this type of authentication to work, the server…
Learn More
-

Meeting AES 256 encryption requirements for data in transit
Overview Not many organizations require AES 256 encryption to secure their sensitive documents. But those who do might find this post quite…
Learn More
-

File transfers have a much bigger impact on Time-To-Market than you think
A growing number of businesses are finding it imperative to get certain products out in the market FAST. To beat extremely tight…
Learn More
-
An introduction to stream ciphers vs. block ciphers
Overview: Stream Ciphers vs. Block Ciphers Secure file transfer protocols like SFTP, FTPS, HTTPS, and WebDAVS encrypt data through symmetric key ciphers.…
Learn More
-
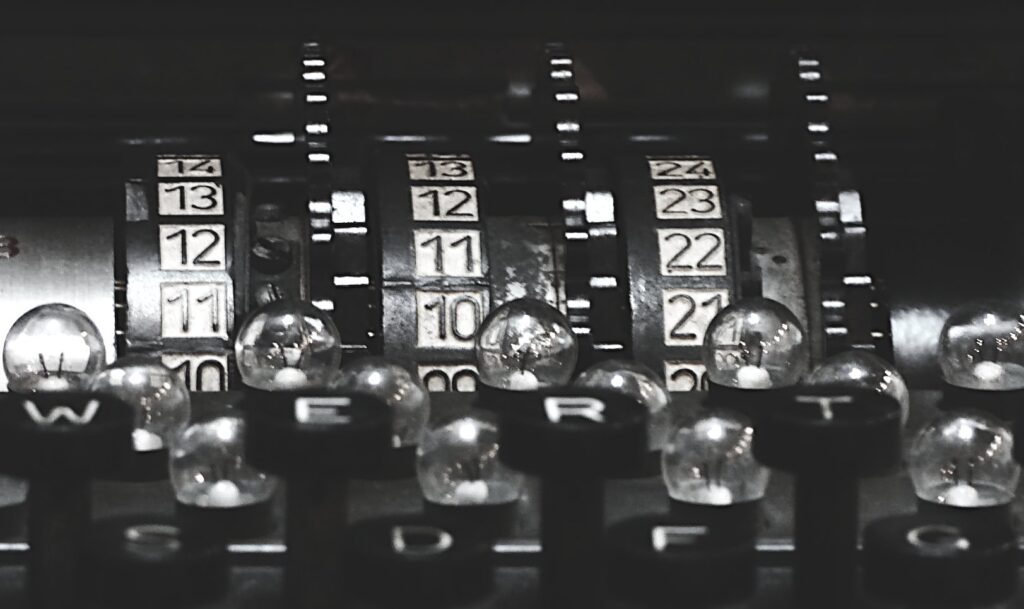
What is a Cipher? | Understanding Encryption Algorithms
Overview The strength of an encryption largely depends on two components: 1) the cipher and 2) the length of the key. We…
Learn More
-

How do digital certificates work – an overview
In our previous post, we discussed what a digital certificate is. But how do digital certificates work? Today, we will give you…
Learn More
-

What Is A Digital Certificate? | Examples of Digital Certificates
Overview: What is a Digital Certificate? When users come to your website, they have a way of telling whether your site is…
Learn More
-

What is a digital signature?
Overview Digital signatures help enforce security during data transfers. They’re mainly responsible for establishing authentication, data integrity, and non-repudiation. Today, we’ll be…
Learn More
-

Understanding hashing
Overview Hashes are essential to secure file transfers. You can find them in operations involving passwords, file integrity checks, digital signatures, digital…
Learn More
-

Symmetric vs asymmetric encryption
Overview: Symmetric vs. Asymmetric Encryption Secure file transfer protocols generally employ a combination of symmetric and asymmetric encryption to preserve the confidentiality…
Learn More
-

How to get an email each time an admin account logs in to your server
Overview A compromised file transfer server admin user account is always a huge problem. In the hands of a person with malicious…
Learn More
-

Why it’s time to disable all versions of SSL
Earlier this month, the PCI SSC (Payment Card Industry Security Standards Council) published a bulletin on impending revisions to PCI DSS (Payment…
Learn More
-
Updated SSH, SFTP and SCP java libraries released
JSCAPE is pleased to announce the release of updated versions of it’s Secure FTP Factory (9.2), Secure iNet Factory (9.3) and SSH…
Learn More
-

PGP encrypting every single file uploaded by members of a group
Overview Some company activities – such as product development or eDiscovery – require a high level of security. The people involved in…
Learn More
-

How to PGP encrypt every single file uploaded by a particular user
Overview Individuals in your organization may have to handle lots of sensitive information. Because there’s always a good chance their files are…
Learn More
-

How to automatically decrypt PGP-Encrypted files upon upload
Overview Whenever PGP files uploaded to your server happen to contain data needed for business processes, you might want to have those…
Learn More
-

Benefits of an SFTP server for business
Overview In today’s data-driven world, the accuracy, integrity, speed, confidentiality, and availability of data matters a lot to businesses. That’s why it’s…
Learn More
-

What is an SFTP key?
Used at the start of a Secure File Transfer Protocol (SFTP) session, an SFTP key is a type of credential you load…
Learn More
-
Benefits of using SFTP on the command line
Overview: SFTP Command Line Although GUI SFTP file transfer clients are more intuitive to use, some people still prefer to use SFTP…
Learn More
-

What is PGP encryption, and how does it work?
What is PGP encryption, and how does it work? Pretty Good Privacy (PGP) encryption protects your enterprise files both in motion and…
Learn More
-

What is an SSL File Transfer? | FTP-SSL | JSCAPE MFT Server
Overview: What is an SSL File Transfer? SSL file transfer is a term sometimes used in referring to a secure file transfer…
Learn More
-

JSCAPE MFT gateway 3.0 released
JSCAPE is pleased to announce the release of JSCAPE MFT Gateway 3.0. This release is a major upgrade from previous versions adding…
Learn More
-
What is OpenID?
Overview Web SSO support comes to JSCAPE MFT Server in the form of two widely accepted standards: OpenID and SAML. Earlier this…
Learn More
-
What is SAML? | Security Assertion Markup Language
Overview: What is SAML? Since version 8.8, JSCAPE MFT Server (now at v9.1) has already supported SAML Web SSO. Although we introduced…
Learn More
-

SSO (Single Sign-On) simplified
Overview There was a time when the average computer user had to enter login credentials only once per day – likely to…
Learn More
-

Guide to PCI DSS compliant file transfers – part 3
In Part 1 and Part 2 of this series we focused on the basics of PCI DSS. Now that you’ve become familiar…
Learn More
-

Guide to PCI DSS compliant file transfers – part 2
Introduction In Guide to PCI DSS Compliant File Transfers – Part 1 you gained a basic understanding of PCI DSS, the data…
Learn More
-

Guide to PCI DSS compliant file transfers – part 1
Overview For the last couple of years, this is the first page you’d find when searching about PCI DSS compliant file transfers.…
Learn More
-
Choosing the right SFTP client for enterprise file transfers
For enterprise organizations, sharing sensitive data is a natural part of business processes. Organizations frequently send files like payroll records, contracts, healthcare…
Learn More
Browse by category
-
(23)
-
(43)
-
(7)
-
(45)
-
(57)
-
(40)
-
(19)
-
(623)
-
(3)
-
(390)
-
(106)
-
(6)
-
(19)
-
(199)
-
(22)
-
(86)



