Category: Secure File Transfer
-

11 proven tactics to safeguard file transfers and prevent data breaches
Learn more from the experts at JSCAPE by Redwood
Learn More
-
How to set up a HTTPS file transfer
Learn more from the experts at JSCAPE by Redwood
Learn More
-

What is MFA authentication and why it’s crucial for file transfer security
Learn more from the experts at JSCAPE by Redwood
Learn More
-

The benefits of secure file transfer software
Any organization that exchanges sensitive files with another party through the internet or any wide area network should carry out those exchanges…
Learn More
-
Fixing SSH/SFTP client connection issues involving Diffie-Hellman-Group1-SHA1
When you’re troubleshooting connectivity issues between Secure Shell (SSH)/Secure File Transfer Protocol (SFTP) clients and servers, it pays to inspect the error…
Learn More
-
What is the fastest way to transfer large files over the internet?
When your business processes involve large files that need to cross the internet in the fastest way possible, look beyond traditional methods…
Learn More
-

13 data security solutions: how data security can be implemented when transferring files
Why do some organizations excel in protecting their sensitive data during file transfers while others fall prey to cyber threats? What constitutes…
Learn More
-
Best file transfer software for mac and PC users
The file transfer software options available today aren’t all created equal. Evaluating solutions based on your organization’s needs goes beyond splitting hairs…
Learn More
-

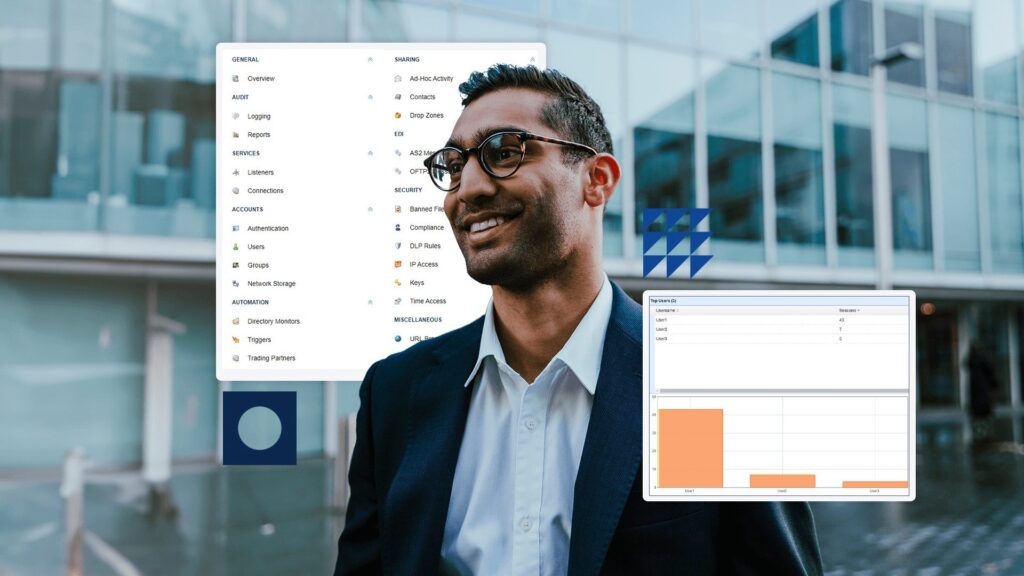
How to simplify IT complexity with a secure file transfer service
In an era dominated by digital transformation and the exchange of sensitive data, the security and efficiency of file transfers have become…
Learn More
-

Finding secure MFT: Considerations for enterprise buyers
Managed file transfer (MFT) is an essential component of secure data exchange for businesses and enterprise organizations. Whether you are transferring sensitive…
Learn More
-

How To Automate An SFTP File Transfer
Automated secure file transfer protocol (SFTP) file transfers are traditionally done through scripts, but there’s a much easier way. In this tutorial,…
Learn More
-
What is AES encryption and how does it work?
Overview: What Is AES? First adopted by the U.S. government to protect classified information, Advanced Encryption Standard (AES) has long gained global…
Learn More
-

How to automatically transfer files from SFTP to azure blob storage via network storage
Let’s say you have trading partners who can only transfer files to you via SFTP. Incidentally, you also happen to have an…
Learn More
-

Three ways to generate OpenPGP keys
JSCAPE MFT Server makes it easy to strengthen secure file transfers with OpenPGP encryption and decryption. But before you can protect your…
Learn More
-

What Is HMAC (Hash-based message authentication code), And How Does It Secure File Transfers?
An Overview of HMAC Data integrity checks are vital to secure communications. They enable communicating parties to verify the integrity and authenticity…
Learn More
-
What is HTTP strict transport security (HSTS)?
When I first read about HSTS, my first reaction was, “What’s this? A replacement for HTTPS? Considering the ubiquity of HTTPS, shouldn’t…
Learn More
-

That free FTP server might cost more than you think
As you scout for the most cost-effective way of transmitting files with your business units and trading partners, among the many file…
Learn More
-

What is client certificate authentication?
Overview How do you strengthen a server’s user authentication system? Well, one solution would be to add another authentication method. Most servers…
Learn More
-

How to set up SSL client authentication
Overview People who use SSL/TLS to secure their online transactions/file transfers are mostly only familiar with two of its security functions: 1.…
Learn More
-
How to install an SFTP server on windows
Because Microsoft Windows doesn’t have a secure file transfer protocol server built in, we’ve put together a simple and easy-to-follow tutorial on…
Learn More
-

Protecting your file transfer service from internal threats
Overview [Last updated: December 2020] Malicious insiders and careless insiders are increasingly posing serious risks to file transfer systems. If nothing is…
Learn More
-

How to securely transfer large files over the internet
Businesses that deal with large files such as high-definition videos, 3D CAD models, and so on, sometimes need to transfer these files…
Learn More
-

Install A Linux SFTP Server Via Command Line And Configure Via Web UI
Overview Let’s say you want to install an SSH FTP server (SFTP) on a Linux machine devoid of a GUI. However, after…
Learn More
-
Using AES-256 to encrypt files you upload to your s3 trading partner
Files you upload to an Amazon S3 trading partner through JSCAPE MFT Server are normally stored in plaintext. If you want to…
Learn More
-
What is AS2 protocol? how to use applicability statement 2
AS2 (Applicability Statement 2) is a secure file transfer protocol used for automated, server-to-server transfers. It ensures message integrity, confidentiality, and reliability,…
Learn More
-

Why and How You Should Verify An SSH/SFTP Client Key’s Fingerprint Before Using It
In one of our previous posts, we talked about the importance of authenticating an SFTP host before logging into it and how…
Learn More
-

Understanding key differences between FTP, FTPS and SFTP
When it comes to moving files across networks, not many protocols are as established as File Transfer Protocol (FTP), File Transfer Protocol…
Learn More
-

How to secure and protect data at rest
To prevent confidential data from leaking out of your organization or getting stolen, your cyber security efforts have to be aimed at…
Learn More
-

How to create a client certificate
In this post, we show you how to configure a client certificate and how to simplify certificate management.
Learn More
-

Benefits of using the JSCAPE MFT server as an AS2 server
As promised in our last post, we’re going to talk about JSCAPE MFT Server and why it’s the perfect choice for an…
Learn More
-

How to pick the best AS2 server for your business
So you’ve already discovered the benefits of AS2 and are now convinced you need one for your business. You might now be…
Learn More
-
What is an AS2 Server? | B2B File Sharing
Last time, we talked about the benefits of AS2 and why you might need it for your business. In order to transact…
Learn More
-

How to apply a digital signature on AS2 MDNs
To ensure non-repudiation of AS2 receipts, you need to affix digital signatures to your AS2 Message Disposition Notifications or MDNs. We’ll teach…
Learn More
-

Applying AS2 Encryption
Overview If your AS2 connection already runs over HTTPS, your EDI messages should already be protected by the data-in-motion encryption that comes…
Learn More
-

Setting up an FTPS server behind a firewall or NAT for PASV mode data transfers
It’s never easy to set up an FTP server the moment firewalls get involved. But it gets even more complicated once you…
Learn More
-

How to install MFT gateway agent on windows
In this post, we’ll walk you through the steps of installing the JSCAPE MFT Gateway Agent on a Windows machine and adding…
Learn More
-

How to install the MFT gateway agent on linux
In this post, we’ll walk you through the steps of installing the JSCAPE MFT Gateway Agent on a Linux machine and adding…
Learn More
-

Using a remote FTP/S service as network storage for your MFT server
JSCAPE MFT Server’s Network Storage module (formerly known as Reverse Proxy) makes it possible to extend the storage of your managed file…
Learn More
-

Setting up a HTTPS to HTTP reverse proxy
Overview Today, we’ll teach you how to set up a HTTPS to HTTP reverse proxy. This service can come in handy if…
Learn More
-

Using a remote SFTP service as network storage for your MFT server
JSCAPE MFT Server’s Network Storage module (formerly known as Reverse Proxy) allows you to utilize various remote services and storage solutions as…
Learn More
-

How to set up an SFTP reverse proxy in JSCAPE MFT gateway
Overview An SFTP reverse proxy adds another layer of security to SFTP services. In addition to SFTP’s ability to encrypt data in…
Learn More
-

MFT security Tip: Use digital certificates for server authentication
For today’s MFT security tip, let’s talk about using digital certificates for server authentication. Ideally, when your users attempt to connect to…
Learn More
-

MFT security tip: replace default admin passwords
For today’s MFT security tip, let’s talk about replacing default admin passwords. Most software applications come with default admin passwords. You normally…
Learn More
-

MFT security tip: encrypting Data-at-Rest
For today’s security tip, we talk about data-at-rest encryption. When your users upload files to your file transfer server, those files are…
Learn More
-

Preparing trading partner servers for SFTP automation
Overview In order to keep transactions secure, you and your trading partners likely use SFTP and other encrypted protocols for your automated…
Learn More
-

MFT security tip: including uppercase and lowercase letters in passwords
In today’s security tip, we talk about including uppercase and lowercase characters in passwords. This is related to our previous video about…
Learn More
-

MFT security tip: use long passwords
It’s time for another MFT Security tip. Today, let’s talk about long passwords and why you would want to require your users…
Learn More
-
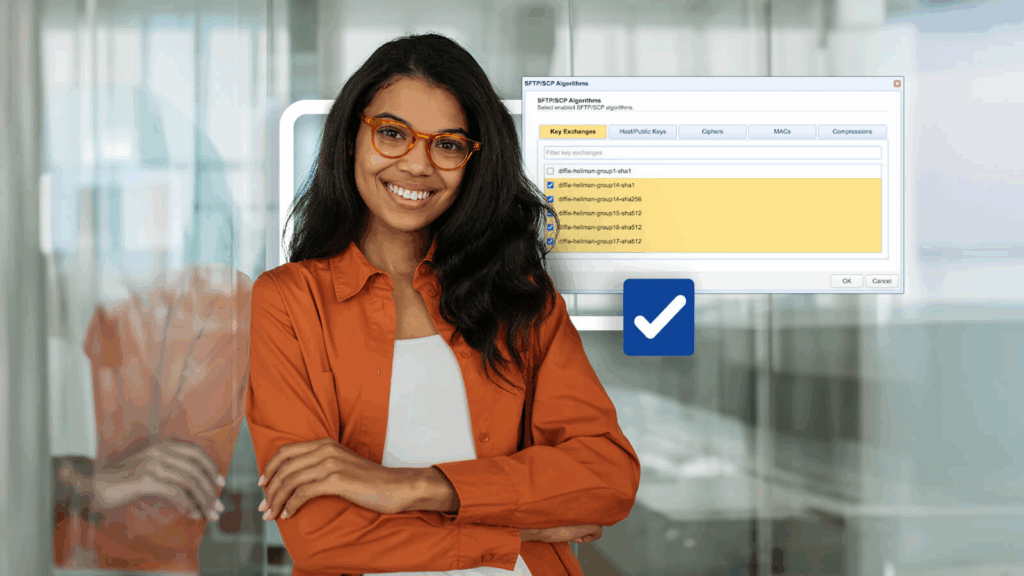
Setting SFTP algorithms on your SFTP server
Overview In this post, we’ll discuss the algorithms in a typical SFTP server and explain their basic functions. We’ll cover algorithms for…
Learn More
-

File transfer security tip: disable FTP
Last week, we published the blog post ‘The Ultimate Guide To Hardening Your Secure File Transfer Server‘, where we shared several tips…
Learn More
Browse by category
-
(23)
-
(43)
-
(7)
-
(45)
-
(57)
-
(40)
-
(19)
-
(623)
-
(3)
-
(390)
-
(106)
-
(6)
-
(19)
-
(199)
-
(22)
-
(86)

